This story was published in September 2015
“A little knowledge is a dangerous thing”. This is a refrain we should keep in mind wherever we can, because a little knowledge is not enough to know just how dangerous we can be. It’s for this reason that I find the subject of online voting so troubling.
As someone who has been writing web applications for years, who has been on the sharp end of penetration tests, and who writes software holding medical records, I know too much about the limitations of the internet to be happy with the notion that we could vote online. It’s a real shame. Like many I do so much online, but like a large number of engineers who build and maintain the various parts of the internet, I know the limits of my craft. It’s time more people did. What follows are the top myths we hear about online voting, and my responses.
Myth #1: We can bank online — why not vote?
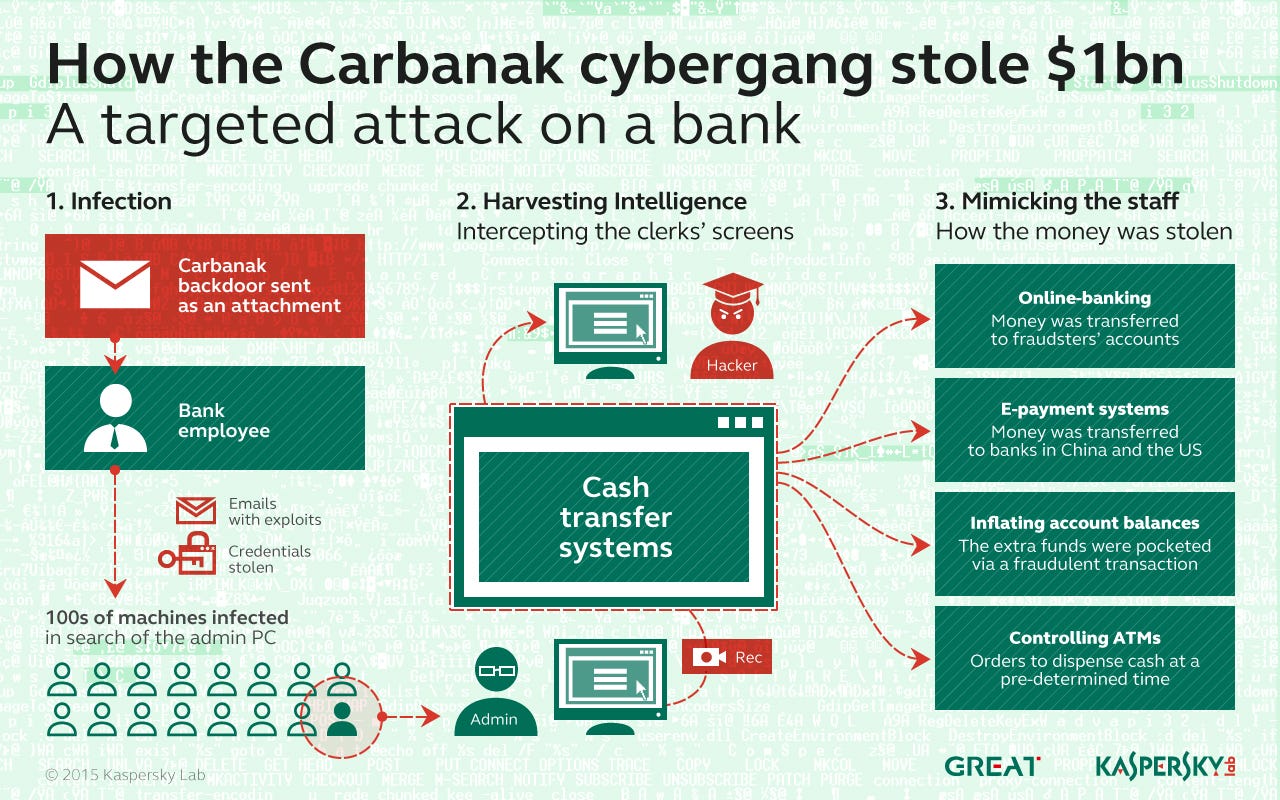
Earlier this year, Kaspersky Lab reported that a hacking gang had (so far) stolen $US1 billion from up to 100 banks in 30 countries over a period spanning two years. They had done this by infiltrating the networks of targeted banks, then lurking in their systems for months, studying the bank’s systems and operations. In some cases, they even turned on the webcams of bank computers, so they could observe staff performing routine operations. Once they had enough information, they would cash out and leave.
It’s hard to decide what the most diabolical part of this operation is. Turning on webcams and logging keystrokes inside a bank’s network is a contender. Making ATMs dispense free money is another. But my personal favourite is that they deliberately limited the amount they stole from each bank, to a maximum of $10 million. It’s like they knew that so many banking systems would be hackable that they limited what they stole so they could do it again and again. Up to 100 times, in fact.
The group is still active (hackers hardly ever get caught), and they’re not the only ones. So, why do most of us feel pretty secure about using online banking? Two reasons: banks run large anti-fraud operations, and banks indemnify us against losses. If a hacker steals your money and you have a good password, it’s not actually your problem. The bank puts some fresh money in your account and you move on.
Now consider voting online, and a bad situation only gets worse. There is no scope for “indemnification against losses”. Furthermore, one of the parties to the voting transaction is supposed to be anonymous. How to verify that an eligible voter cast a vote that arrives at a voting system’s door remains an unsolved problem. They may have sent the correct credentials, but who is to say it was them who was doing the voting, and not some “helpful” malware installed on their computer?
In a close election, paper is king. The 2011 general election had one of the closest results in NZ history, when Paula Bennett won Waitakere by just 9 votes after a judicial recount. That means, they got the paper ballots out and counted them in a courtroom, with a judge and scrutineers overseeing the process. And at the end, everybody agreed with the result. Good luck with that when you have an online voting system, and malware to manipulate votes is discovered on many New Zealanders’ computers a day after the results have been declared.
Myth #2: Online voting will result in cost savings
I know I’m at risk of pointing out the bleeding obvious here, but we will continue to have to offer the paper ballots as long as a reasonable portion of people are not online. It could be a generation until everyone is online, and in the mean time, we have to run both methods of voting.
Technology moves so fast that computer systems built today need constant maintenance, monitoring and patching just to keep them operational. In the case of an online voting system, defences against the latest threats and constantly upgrading underlying software and operating systems will make the cost even higher than for the average system. It’s likely the budget for these systems will be in the millions of dollars a year.
Consider how successful we have been at such endeavours previously. Most New Zealanders are familiar with the Novopay debacle — a system that failed so spectacularly, the government actually had to appoint a Minister to the task of getting it barely working again.
Myth #3: Online voting will increase turnout
The evidence for this is thin. While a correlation has been shown in Estonia, a causation has not, and detailed studies attempting to account for all of the variables in play have not shown a direct link.
This absence of good evidence is the reason why the Online Voting Working Group’s report can only say that online voting “.. has the potential to enhance participation”. It also “has the potential” to get hacked. One of these has more evidence than the other.
Statistics New Zealand have already surveyed New Zealanders about their reasons for not voting. The main one? “21 percent of non-voters said they did not vote in the 2011 General Election because they ‘didn’t get round to it, forgot or were not interested’ to vote.”. In a word, disengagement.
The “missing million” has been talked about for a long time in New Zealand — the supposed million voters who don’t bother to vote every election. If we have data saying that the main reason for this is disengagement, and no data worldwide suggesting that online voting increases turnout, why would we attempt to address the latter problem? Would it not make sense to focus more effort on the former? We could draw a lesson or two from the Swedish example: “the task of getting people to participate must be a constant, year-round focus of attention, not just an issue of concern at election time.”
Myth #4: All voting systems have risks
…but online voting is categorically worse.
This line is often pedalled by vendors wanting to sell you a solution, while they downplay the risks of online voting and remind you that fraud can happen with the paper ballot. I hope you are not so credulous as to take them at their word.
What is missing from an online vote is a paper trail — actual paper that can be counted again if a result comes into dispute. With an online system, it’s impossible to trust the results of the count, let alone a recount. A programming error could lead to an incorrect count, and nobody would know. A system administrator could be threatened, and maliciously tamper with the results, and nobody would know. Or malware could be discovered on the computers of thousands of New Zealanders, that when studied clearly has the purpose of modifying how the online voting website looks so that people think they’re voting for one candidate when they’re actually voting for another.
With a paper ballot, none of these things are concerns. Scrutineers oversee the whole process, and a judicial recount can be ordered in the case of a dispute. There is also no scope for hackers to “raise our turnout”.
At the 2014 general election, the fraud rate was measured at 0.004%. Out of 2,416,479 votes, that leaves us with… 96. About 1.5 per electorate. It’s likely at least of the “fraudulent” votes were accidents — e.g. the wrong name being crossed off in the book by a poll clerk. And if it had come to light that these votes had mattered, we would have just done a judicial recount. Granted, the postal voting system used for local body elections is different — and incorporates more risk. It simply doesn’t include the risk that foreign gangsters could have a go at ruining our elections without even being on New Zealand soil.
What I personally feel is risky, is spending millions of dollars on making our system more vulnerable, when there’s no good evidence it will increase turnout.
Myth #5: Technology can fix the technology problems
Even if this were true, even if we could build a hack- and DDoS-resistant system that somehow stored everybody’s votes without storing who everybody voted for (the “secret” part of “secret ballot”), this only solves part of the overall problem — and the other parts are far harder to solve. They may be completely unsolvable, in fact.
Consider the environment our perfect online voting system is deployed into. The client devices that connect to it — that’s our computers, phones and so on — are completely compromised. Malware infests a large proportion of our computers, controlled by the thousand and marshalled into sending the spam we constantly receive performing the DDoS attacks we hear about, and maybe one day, voting for us.
Our perfect online voting system will only ever be able to see the data it is sent. These credentials, these votes, from this browser and IP address, which has accessed our system this many times before. What our system can’t do, is verify that our voters clicked on what they thought they did (hint: malware can change web pages), or rely upon showing the voters their choices later (not only did we just break the “secret” part of secret ballot, but our malware is back and changing pages again).
But that’s still not all. Scrutineers are told to watch out for husbands hovering over their wives at polling booths. In an abusive household, the victim has no right of secrecy, making coercion by abusive or judgemental people far easier. Outright vote selling also becomes simple. And in families with voting-age children living at home with their parents and disengaged with the election process, maybe a parent will decide that one extra vote for them won’t hurt?
With voting processes involving paper, the lack of technology is a feature. It’s too hard for one person to manipulate thousands of votes. The high friction of a polling booth in particular prevents the kinds of casual fraud that even a perfect online system would have the unintentional effect of enabling.
Myth #6: Online voting is inevitable
This is a feeling that people unskilled in building systems for the internet have, in the same way that physicists probably get tired of hearing about teleportation. People can get excited, allocate funds, steer public policy and talk optimistically all they like, but when you listen to the people most qualified to do the work, you’re not going anywhere.
Online voting getting hacked. Now that, I feel safe to say, is inevitable.



